Trojan.Ransom
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 9 |
| First Seen: | January 19, 2011 |
| OS(es) Affected: | Windows |
Trojan.Ransom is a generic name for a kind of malware that locks up the infected PC and demands a ransom in order to unlock it. Variations on this kind of malware will often have “Trojan.Ransom" in their names, along with some other words or numbers and letters, to identify each specific malicious file. However, when the malware is referred to only as Trojan.Ransom, it tends to be an infection that locks the infected computer with a screen that includes pornographic content or references to pornographic content. In that case, Trojan.Ransom is widely referred to as WinLock or LockScreen.
Table of Contents
Why is It so Common for Trojan.Ransom’s Lock Screen to be in Russian?
Trojan.Ransom has become more and more of a problem with time, and infection rates are higher now than they have ever been, but Trojan.Ransom is actually nothing new. The first reports of infections were in September 2004. For at least the first two or three years, infections of Trojan.Ransom were almost exclusive to Russia, and historically, Russian PC users have been hit the hardest by the Trojan.Ransom scam. Eventually, varieties of Trojan.Ransom spread to computers around the globe, although Russian-language versions of the malware still seem to be much more common than any other kind. This means that it is typical for people to wind up with a version of the Trojan.Ransom infection that is in a language they don't understand, adding difficulty and confusion to the malware removal process.
Symptoms Caused by Trojan.Ransom
Trojan.Ransom is characterized by one major, characteristic symptom, which is that Trojan.Ransom locks the infected PC with a screen that references pornography and demands a ransom payment in order to unlock the system. While Trojan.Ransom is present and active, Trojan.Ransom will lock the affected PC as soon as the computer starts, completely preventing access to everything, including the desktop. While the specific wording of the lock screen varies from one variety of Trojan.Ransom to the next, the content generally follows one of two closely-related patterns:
- The lock screen claims to represent a government agency, or threatens to report the user to a government agency. This issue is a supposed crime relating to pornography, especially varieties of extreme or unusual pornography that are illegal. The lock screen claims to have evidence against the user, either in the form of browser history or hard drive contents, implicating the user in viewing or possessing illegal pornographic content.
- The lock screen claims that the user is required to pay a fine to the government, or it demands that the user pay some amount of money in exchange for not being turned over to the government. There is a specific, very short time limit for the payment of the fine or ransom. Twenty-four hours is most common. After that, supposedly, either the government will arrest the user, or whoever possesses the evidence against the user will give it to the government.
- The lockscreen claims to represent a service or community that specializes in a variety of pornography that the user will most likely find repellent. It claims that the user has agreed to a certain term of membership and that the membership agreement included a penalty for cancelling early. In order to unlock the computer, the lock screen demands that the user pay this supposedly previously-agreed-upon cancellation fee. As with the previous scenario, there is often a limited time frame for payment of the fee, and untraceable payment methods are always used.
A method of payment is specified for the ransom, and it is never by credit card. Untraceable payment services such as cash cards and money sent via text message are standard.
Good Reasons Not to Pay the Trojan.Ransom Ransom
There have been varying reports about the effects of paying the ransom that Trojan.Ransom demands. Some users report that their computer was unlocked for a day or two, only to be locked again; others report that paying the ransom has no effect whatsoever on the state of their PC. Either way, paying the money that Trojan.Ransom asks for is not worthwhile, since Trojan.Ransom doesn't result in the malware permanently leaving you alone.
The good thing about removing Trojan.Ransom is that it is relatively simple to do, because regardless of which mutation or variety is causing a particular infection, Trojan.Ransom is not at all a sophisticated piece of malware. On the contrary, Trojan.Ransom is often simplistic and crude under the surface, which can be a result of the malware being created by crooks who are only very minimally competent in creating these programs. So, rather than panicking and paying them money that you will never be able to get back or to prove that you sent, remember that what the lock screen tells you is fake. Trojan.Ransom will not control your computer forever.
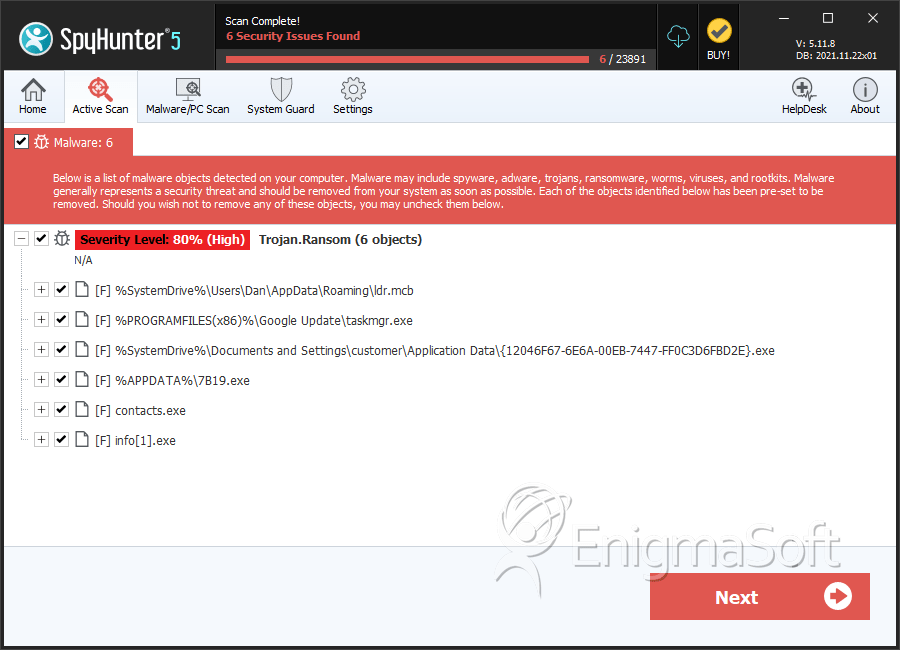
SpyHunter Detects & Remove Trojan.Ransom
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | ldr.mcb | f3b519a1b7d8f7111a2a0ba1f5674e38 | 4 |
| 2. | taskmgr.exe | de095d328199bb85a6d542a7dceacfae | 2 |
| 3. | {12046F67-6E6A-00EB-7447-FF0C3D6FBD2E}.exe | 322bc1ddf691b8a9f7815ac1f4b9e9b7 | 2 |
| 4. | 7B19.exe | 843247f84615f30bc9fdbe1e074acc24 | 1 |
| 5. | contacts.exe | dcc4501e3348c4665391ff126d7c2fb1 | 0 |
| 6. | info[1].exe | 270b8ce04a9f55809938430a2fe6bb47 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.