Trojan.Alureon.D
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 399 |
| First Seen: | November 30, 2010 |
| OS(es) Affected: | Windows |
According to ESG security researchers, Trojan.Alureon.D is considered one of the most dangerous malware infections present in the wild. Trojan.Alureon.D can be used to monitor a computer's online activity and to steal sensitive information, such as that data relating to online banking and credit card transactions. Trojan.Alureon.D has also been responsible for various attacks on the Windows Operating system and, in fact, many of Microsoft's updates for their operating systems were implemented in order to counteract this dangerous infection's effects. In the past years, the largest botnets in the world have used Trojan.Alureon.D in order to infect their victims' computer systems, resulting in various DDoS attacks and the sending of massive amounts of spam email from infected computers.
Table of Contents
A Brief History of Trojan.Alureon.D
The first cases of Trojan.Alureon.D infections first appeared in 2006. The main danger of the Trojan.Alureon.D infection lies in its rootkit component, which can hide completely from detection. Typically, the Trojan.Alureon.D infection was first used to install rogue security applications on the victims' computer (for example, Security Essentials 2011 or Internet Antivirus 2011). Trojan.Alureon.D is designed to take over the spoolsv.exe service in the Windows operating system. Once Trojan.Alureon.D does this, Trojan.Alureon.D can then corrupt your computer's drivers (for example, atapi.sys), which then lets Trojan.Alureon.D implement its rootkit component. Usually, a Trojan.Alureon.D infection will manifest itself through a browser hijacker and, in recent years, this malware infection has been used as an essential component in the fake search engine online scam. Throughout its history, variants of Trojan.Alureon.D have also shown the capacity to disable Windows Update and to block the infected computer's security software.
Protecting Your Computer From Trojan.Alureon.D
According to ESG security researchers, it is essential to ensure that your operating system is completely updated, since many of the official patches are meant to prevent Trojan.Alureon.D attacks. ESG malware researchers have also noted that Trojan.Alureon.D also has the capacity to bypass certain Windows 7 security measures, making Trojan.Alureon.D particularly difficult. Trojan.Alureon.D can remain on an infected computer system indefinitely without being detected. ESG security analysts recommend a specialized rootkit-removal tool to deal with Trojan.Alureon.D infection. As is the case with most Trojans, the best protection against Trojan.Alureon.D is prevention through the judicious use of a reliable anti-malware scanner and good judgment when going online. It is also important to note that this malware infection will rarely attack alone, requiring the removal of various other Trojans that may have entered your computer system as a result of a Trojan.Alureon.D infection.
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Panda | Generic Trojan |
| AVG | Generic16.BRWH |
| Symantec | Hacktool.Rootkit |
| Sophos | Mal/Generic-A |
| TrendMicro | BKDR_TIDIES.SMA |
| AntiVir | TR/Agent.42496.27 |
| BitDefender | Trojan.Generic.3238155 |
| Avast | Win32:Jifas-DT |
| NOD32 | a variant of Win32/Olmarik.SR |
| CAT-QuickHeal | Trojan.Agent.ATV |
| McAfee+Artemis | DNSChanger!dd |
| eTrust-Vet | Win32/ASuspect.HGOJO |
| AntiVir | TR/Crypt.XPACK.Gen3 |
| NOD32 | Win32/Olmarik.XH |
| Avast | Win32:Rootkit-gen |
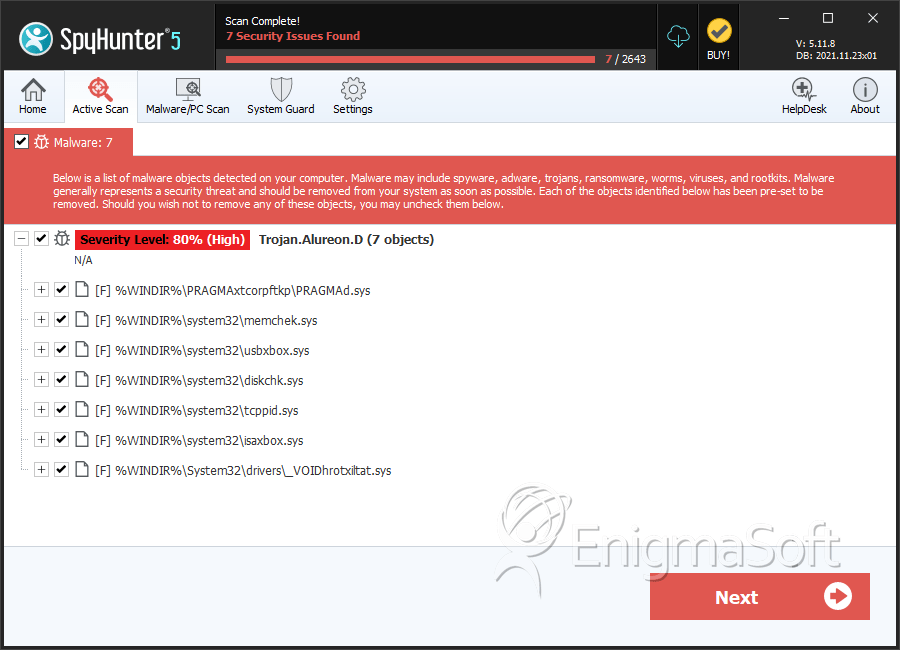
SpyHunter Detects & Remove Trojan.Alureon.D
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | PRAGMAd.sys | 4fc1255817092de5c285440cf477035e | 98 |
| 2. | PRAGMAd.sys | afc6795bb909749f446f57e36f7b33e3 | 64 |
| 3. | PRAGMAd.sys | 4a2dccdd2a14acce0dc2bcfc01b01b15 | 46 |
| 4. | PRAGMAd.sys | 1d177f19440f4b4be104adcce3341685 | 30 |
| 5. | PRAGMAd.sys | fd8913513a87ed566c8c47f7cf2961c0 | 25 |
| 6. | PRAGMAd.sys | 421af6709d670e5b97a8c37e80144343 | 22 |
| 7. | memchek.sys | 1ca0d8ee82db8012de42b16f2ef69674 | 14 |
| 8. | usbxbox.sys | b3da42dfcd9851c24c9b09b8c188266d | 13 |
| 9. | diskchk.sys | e94d859753bb68f113b88e8b78607776 | 11 |
| 10. | PRAGMAd.sys | 4a672d94142ea8056ff589377fb8339b | 10 |
| 11. | PRAGMAd.sys | 0d72febb1914c0d7a379b9cc2f6bb8ff | 10 |
| 12. | PRAGMAd.sys | a3f92e9bf557198dc39d4045d2ec2144 | 8 |
| 13. | PRAGMAd.sys | 0aeb71ef75d921539e6e02dfa2c12e08 | 8 |
| 14. | tcppid.sys | c72311b8d604a3e3e9b36df733f30843 | 7 |
| 15. | PRAGMAd.sys | 184110fe4f5c6a4416b9decee90a2d9f | 6 |
| 16. | isaxbox.sys | 5a7eef7dcdae6912afe7f50983d5520f | 5 |
| 17. | PRAGMAd.sys | c907276d48943001a4745b6d4e254c13 | 3 |
| 18. | PRAGMAd.sys | 9d39fe1b36199d5717cae14ed3680e67 | 3 |
| 19. | PRAGMAd.sys | e671ab67d233cb4e87b1b679a92a0ed0 | 2 |
| 20. | PRAGMAd.sys | e2c5ffec5eb9612eea2d5ce22fdcfe09 | 2 |
| 21. | PRAGMAd.sys | b52194d21487e3cf2178950228552ac5 | 2 |
| 22. | PRAGMAd.sys | aca6e953ff8d2f536fd1d297e0486734 | 2 |
| 23. | PRAGMAd.sys | 2b5b356793a655697edd8c58b2964fe2 | 2 |
| 24. | PRAGMAd.sys | f4c09fd7833565264f8feb1349a558a1 | 1 |
| 25. | PRAGMAd.sys | 0cc76a2452fabfa4d6e98082d415201e | 1 |
| 26. | PRAGMAd.sys | 90046fd8e3bee623a26dfccb6a602746 | 1 |
| 27. | _VOIDhrotxiltat.sys | 89b56f6143f7c1ad44cd10f46700b9da | 1 |
| 28. | usbxbox.sys | ||
| 29. | TDDS.sys | ||
| 30. | UACD.sys | ||
| 31. | memchek.sys |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.