Internet Security 2011
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 34 |
| First Seen: | December 20, 2010 |
| Last Seen: | August 17, 2022 |
| OS(es) Affected: | Windows |
Internet Security 2011 Image
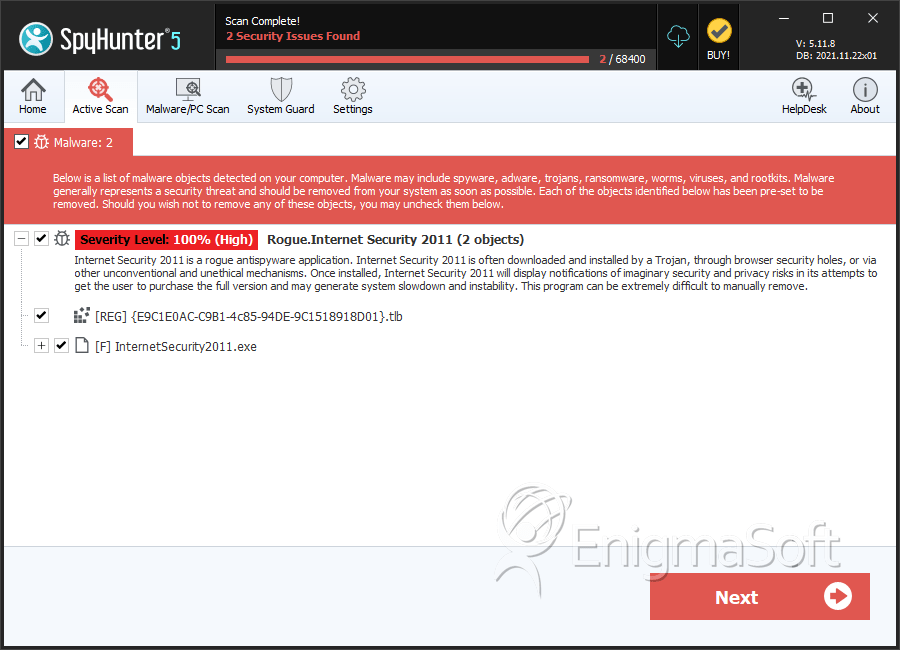
Internet Security 2011 is a rogue security application created by cyber-criminals to trick victims into giving their hard earned money by charging to remove non-existent threats. Once inside a computer, Internet Security 2011 will launch a bogus online system scan alleging that the system is infested with malware. Internet Security 2011 is a variant of Antivirus 2010 and generates alarming warning alerts that advise the victim to purchase its “full” version in order to remove the “detected” threats.
Internet Security 2011 comes bundled with a rootkit that prevents you from opening any programs. Any attempt to open a program on your PC will give you the following message: “Windows cannot access the specified device, path, or file. You may not have the appropriate permissions to access the item.” or “Access Denied.” Internet users might unknowingly download the rootkit, which comes with a rogue anti-spyware application like Internet Security 2011, from freeware or fake video codecs downloaded from torrent websites. The rootkit is able to block programs, even legitimate anti-virus/anti-spyware programs, from executing by changing the security permissions on the executable.
Because Internet Security 2011 will not allow access to various other programs installed on the infected computer, it could be said that Internet Security 2011 may render the affected computer virtually useless. Other malware parasites have been known to populate PCs that have Internet Security 2011 installed on them. These malware parasites could range from rootkits to other rogue anti-spyware programs that are somewhat similar to Internet Security 2011 in their blocking abilities.
To modify the permissions and be able to open your programs, use the command line tool cacls.exe from Windows. Just open your Command Prompt and type the following command:
cacls [complete path to the program] /G Everyone:F
To open anti-malware program SpyHunter so it’s able to detect Internet Security 2011 on your PC, type the following command:
cacls “C:\Program Files\Enigma Software Group\SpyHunter\SpyHunter.exe” /G Everyone:F
The [complete path to the program] variable means to add the path of the program file you want to open. Internet Security 2011 is unable to detect or remove malware, therefore do not trust any alert messages displayed by it and have it removed from your PC immediately.
Table of Contents
How to Install SpyHunter on a PC Infected with Internet Security 2011
Internet Security 2011 blocks the installation of trusted security applications. To install SpyHunter on a PC infected with Internet Security 2011, follow the instructions below:
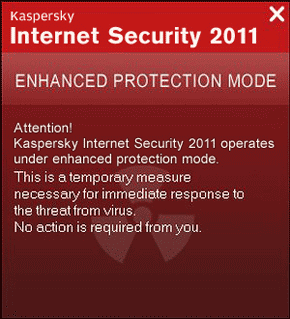
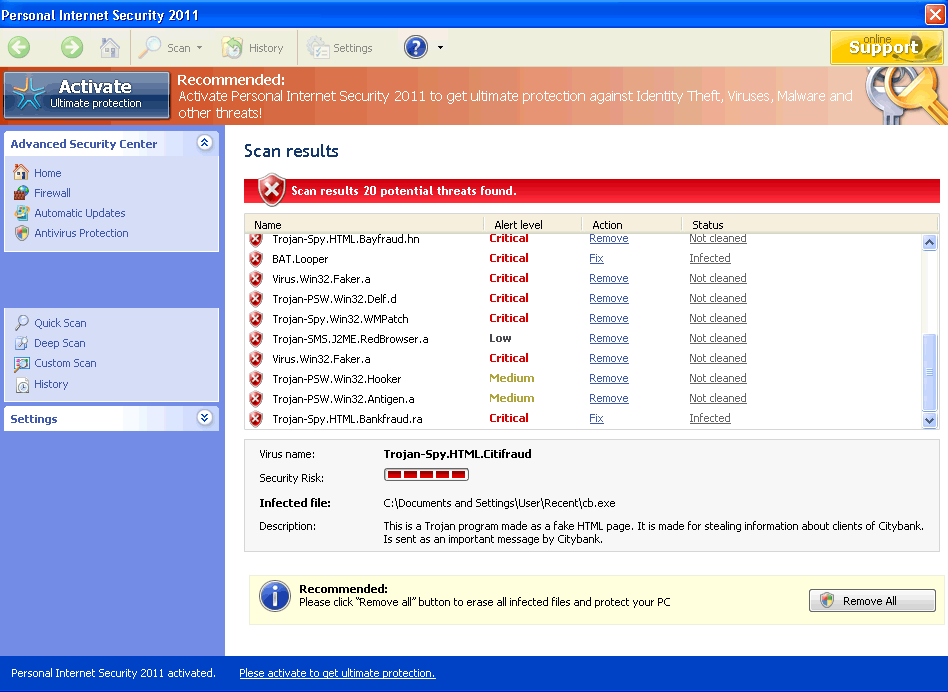
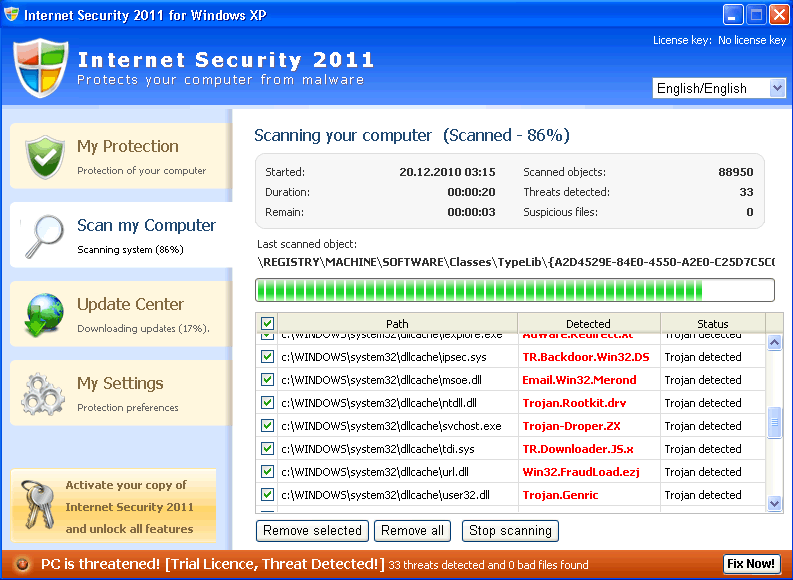
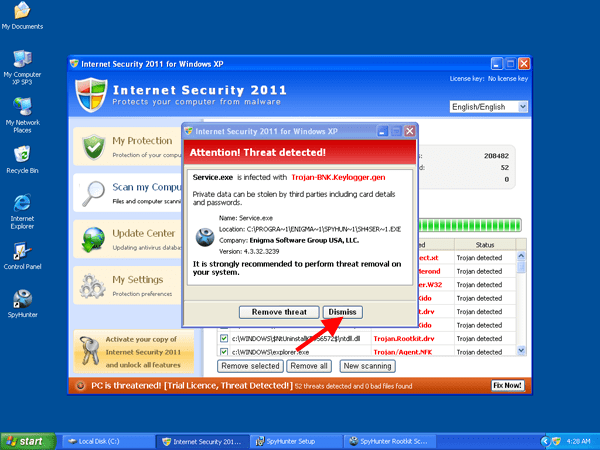
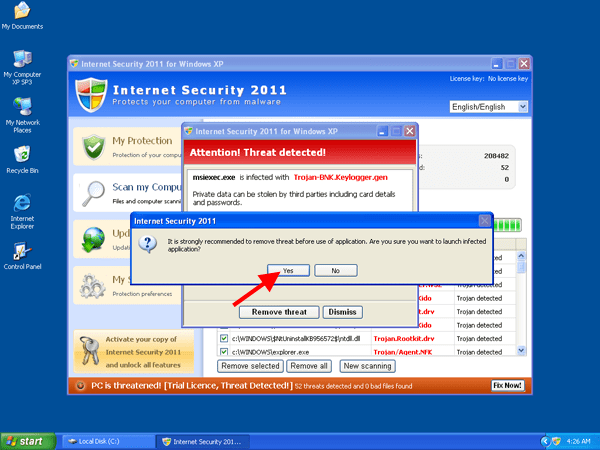
- When Internet Security 2011 prompts a fake alert similar to the windows listed in Figure 1, 2 , 3, or 4, select the option 'Dismiss'. Clicking on the 'Dismiss' button will ensure Internet Security 2011 does not stop the installation of SpyHunter.
Figure 1.
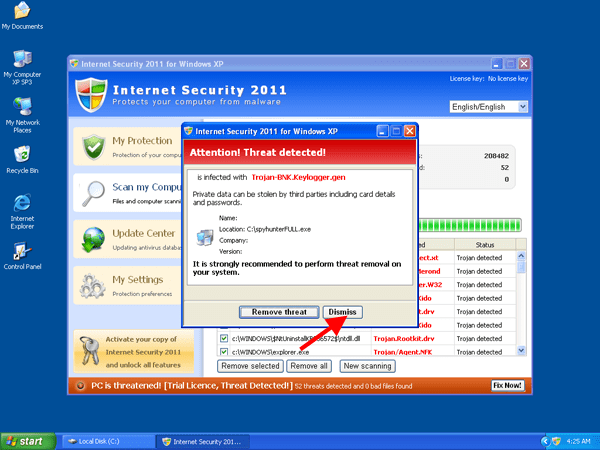
Figure 2.
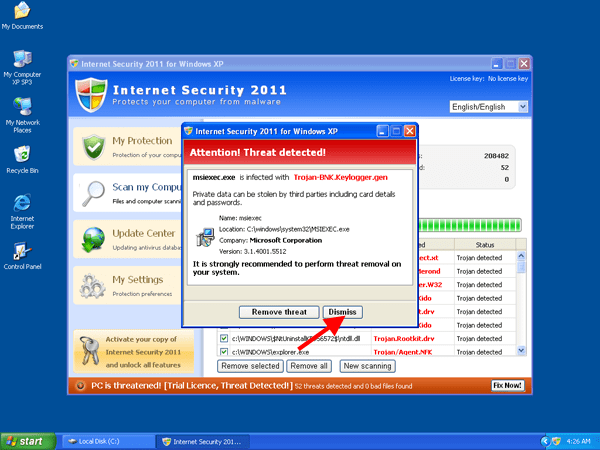
Figure 3.
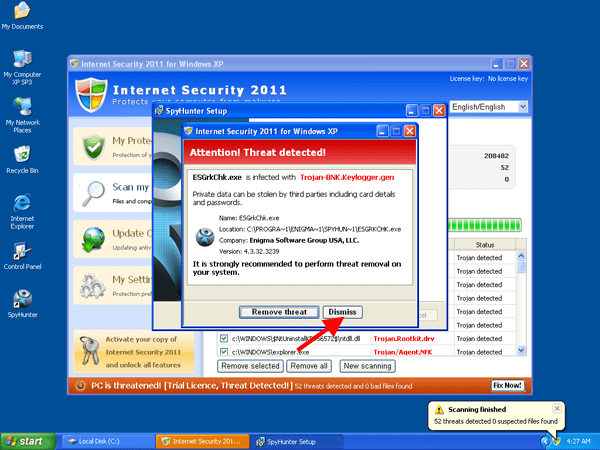
Figure 4.
- After selecting 'Dismiss', select 'YES' when the Internet Security 2011 message appears saying 'It is strongly recommended to remove threat before use of application' as shown in Figure 5 or Figure 6.
Figure 5.
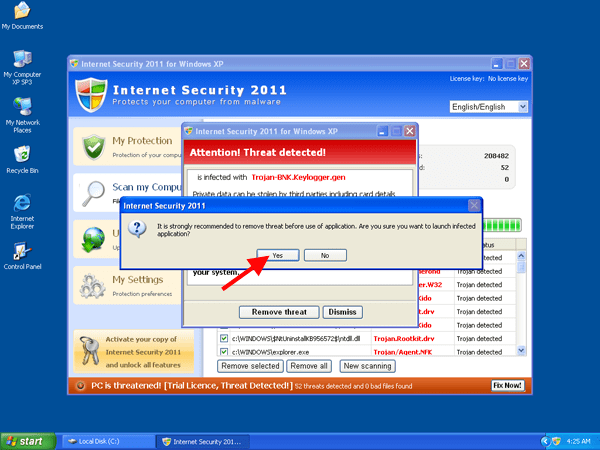
Figure 6.
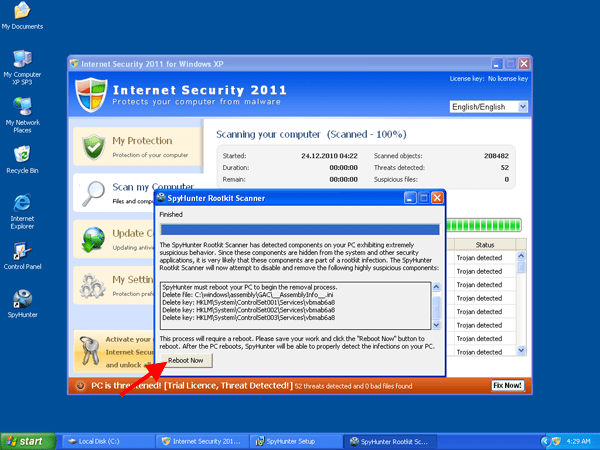
- Once you've installed SpyHunter, you will be prompted from the SpyHunter rootkit scanner to reboot your computer. Select 'Reboot Now' as shown in Figure 7.
Figure 7.
- After reboot of your computer has completed, SpyHunter will automatically launch and scan your system. Once the system scan has finished, select the 'REMOVE ALL THREATS' option.
- After all threats have been removed, you will be asked to reboot your computer once more. Select 'Restart PC' as shown in Figure 8.
Figure 8.
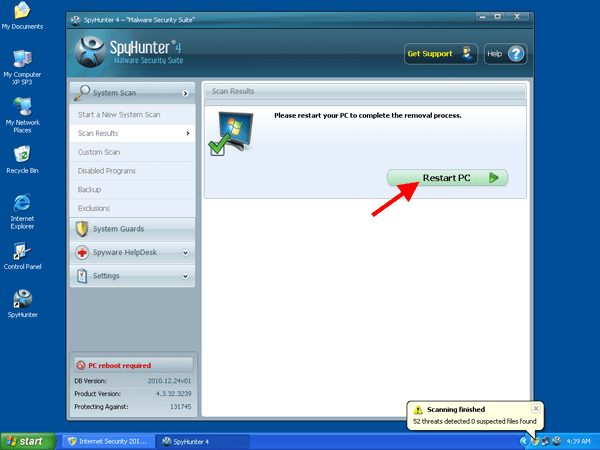
- After the second reboot of your computer all threats should have been removed and your system should be clean and free from Internet Security 2011.
SpyHunter Detects & Remove Internet Security 2011
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | InternetSecurity2011.exe | 1e04058ca548ab32cef1b6fd23808144 | 1 |
| 2. | C:\Windows\System32\drivers\vbma22b4.sys | ||
| 3. | C:\Windows\System32\mswmqnei.dll | ||
| 4. | C:\Windows\System32\exefile.exe | ||
| 5. | C:\Windows\WinSxS\x86_Microsoft.Windows.Shell.HWEventDetector_6595b64144ccf1df_5.2.2.3_x-ww_5390e909\shsvcs.dll |