CryptInject
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 16,404 |
| Threat Level: | 90 % (High) |
| Infected Computers: | 68 |
| First Seen: | July 24, 2009 |
| Last Seen: | July 27, 2023 |
| OS(es) Affected: | Windows |
CryptInject is a heuristic detection used by the Microsoft Defender (previously named Windows Defender) to flag items that display characteristics usually associated with Trojan Horse malware threats. The full detection that is likely to be displayed to users is Trojan:Win32/CryptInject!ml. Heuristic detections examine the behavior of the examined application and signify that it has suspicious aspects. However, this doesn't necessarily mean that the flagged item is threatening. In many cases, the security alert is a false positive and the item is incorrectly determined to be malware.
However, it is better not to take any chances when it comes to Trojans. This category of malware threats is exceptionally versatile. Threat actors can utilize Trojans in numerous, different attack campaigns and modify them to perform specific, invasive actions that match the goals of each operation. Trojan threats can collect and transmit data obtained from the infected system, establish a backdoor connection to the device, run keylogging routines capturing all pressed keys and more.
Trojans are often used as delivery systems for the final payloads that the attackers wish to deploy on the breached devices. They can fetch and execute more specialized malware threats, such as spyware, crypt-mniners, ransomware, etc.
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Sunbelt | Packed.Win32.NSAnti.e |
| Prevx1 | Cloaked Malware |
| F-Secure | Suspicious:W32/Malware!Gemini |
| TrendMicro | PAK_Generic.001 |
| Symantec | Downloader |
| Sunbelt | Trojan.Vxgame.z |
| Panda | Trj/Spammer.AJD |
| NOD32 | Win32/TrojanDownloader.Agent.XLW |
| McAfee | Downloader-BKB |
| Fortinet | W32/Agent.YGY!tr.dldr |
| F-Secure | Trojan-Downloader.Win32.Agent.ygy |
| Comodo | Unclassified Malware |
| ClamAV | Trojan.Downloader-51334 |
| CAT-QuickHeal | TrojanDownloader.Agent.ygy |
| BitDefender | Trojan.Downloader.Agent.ZMW |
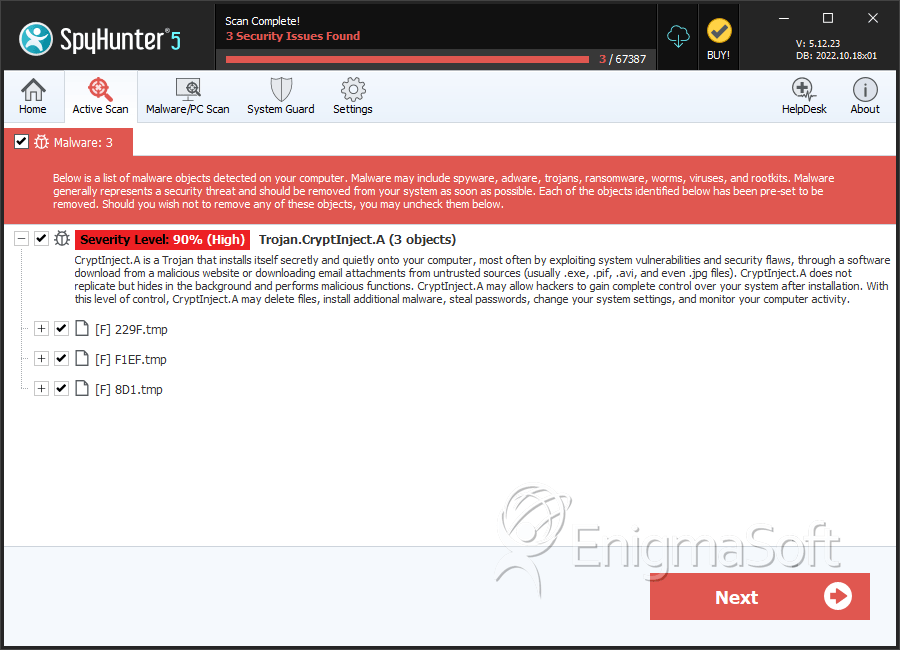
SpyHunter Detects & Remove CryptInject
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | 229F.tmp | 031904d53580fcccf3cc26a5075d8677 | 0 |
| 2. | F1EF.tmp | 87e87d15428a07a5939c3ecb30c63e49 | 0 |
| 3. | 8D1.tmp | 6d6aa01a0ae23b5a6d3926c9d6a84133 | 0 |

