Backdoor.DarkKomet
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 6,687 |
| Threat Level: | 60 % (Medium) |
| Infected Computers: | 49,352 |
| First Seen: | May 20, 2013 |
| Last Seen: | February 3, 2026 |
| OS(es) Affected: | Windows |
Table of Contents
Aliases
12 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| Panda | Trj/CI.A |
| AVG | BackDoor.Generic17.FPU |
| Fortinet | W32/DarkKomet.ALBZ!tr.bdr |
| Ikarus | Backdoor.Win32.DarkKomet |
| TrendMicro | TROJ_GEN.RCBZ7EE |
| AntiVir | TR/Rogue.987207 |
| Comodo | UnclassifiedMalware |
| Kaspersky | Backdoor.Win32.DarkKomet.albz |
| Symantec | WS.Reputation.1 |
| McAfee | Artemis!93B88D2FD387 |
| McAfee-GW-Edition | Heuristic.LooksLike.Win32.Suspicious.B |
| Kaspersky | UDS:DangerousObject.Multi.Generic |
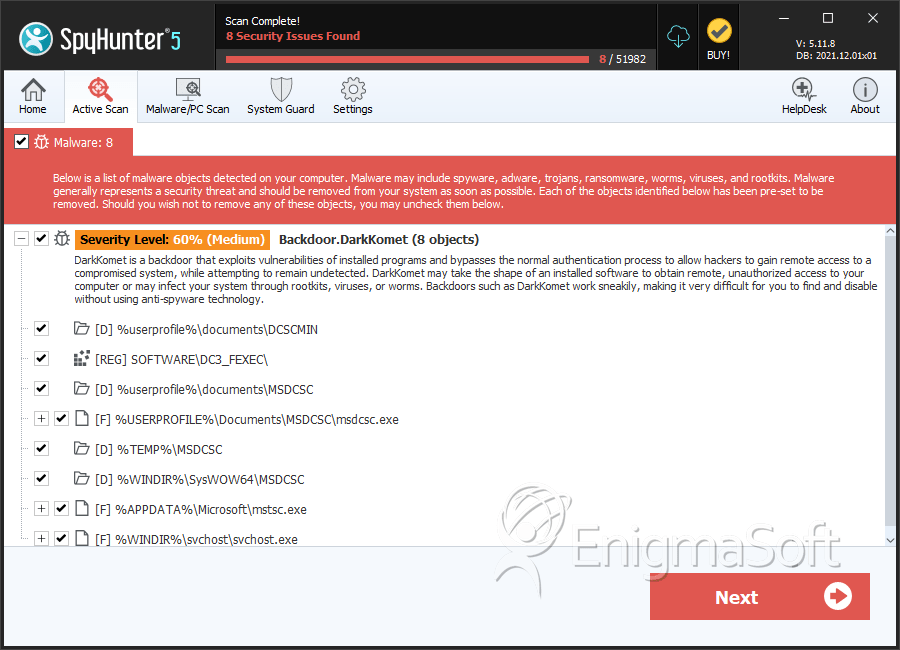
SpyHunter Detects & Remove Backdoor.DarkKomet
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | svchost.exe | 2bef02594106e27d81a17a885c9efe0d | 165 |
| 2. | M.exe | 40527d9f884efd415be418046ba328d3 | 42 |
| 3. | msdcsc.exe | 3e9d8a8cbf59bbfa1f8417d190d8414d | 40 |
| 4. | mstsc.exe | f5636b4f322154aaf28d6143fd17ea39 | 30 |
| 5. | windefender.exe | 4aa28c33b7dae76750e215a90e378f09 | 20 |
| 6. | service.exe | 53fbd2492211dba078aa8aaf1c807f0e | 19 |
| 7. | WMPUpd.exe | 1e9e9cdec7282d81bc8c891dc6047463 | 1 |
| 8. | steamservice.exe | 27eea7c653a1f397f55fca8e0826c764 | 1 |
| 9. | exossec.vbs | 656c840fc9837ec0437ef31ad4bb33a1 | 1 |
| 10. | file.exe | f0824e67a6528161903f57db61401d63 | 0 |
Registry Details
Directories
Backdoor.DarkKomet may create the following directory or directories:
| %ALLUSERSPROFILE%\Microsoft\Windows\Start Menu\MSDCSC |
| %ALLUSERSPROFILE%\Microsoft\Windows\Start Menu\Programs\MSDCSC |
| %HOMEDRIVE%\MSDCSC |
| %TEMP%\MSDCSC |
| %WINDIR%\SysWOW64\MSDCSC |
| %WINDIR%\System32\MSDCSC |
| %WINDIR%\msdcsc |
| %userprofile%\documents\DCSCMIN |
| %userprofile%\documents\MSDCSC |
| %userprofile%\my documents\DCSCMIN |
| %userprofile%\my documents\MSDCSC |
Analysis Report
General information
| Family Name: | Backdoor.DarkKomet |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
8ade86169f72debfa2856a204570bc86
SHA1:
4aa5ae05adb93b1efb9c62185db93e03c1423062
SHA256:
6DC7651572EB624CBE2BBCB7E4671173D976CB227D773B10072D1D1AF5DFF8B6
File Size:
20.49 KB, 20492 bytes
|
|
MD5:
ce7fb57a3b14632099182ed22a642c94
SHA1:
db04328f6d3030ff0d6ce91c949bb07d95296206
SHA256:
39D039FE513ECB09D5D256ACF1B0D7896184DEBF30BDBA2007704D3DA5D0E046
File Size:
20.49 KB, 20492 bytes
|
|
MD5:
9560a2bd525f945172c6a397b58258bc
SHA1:
fda00deb4bfb93437976b89c7568680112ddf0f9
SHA256:
913713B998882A233F4853E4054D1C36AB8167783928433ACD40053BD96F7A54
File Size:
20.49 KB, 20492 bytes
|
|
MD5:
521866c4f74403aa18aa6940074b14f0
SHA1:
c6db2f6b962234b1e34beef8705b5c301e016070
SHA256:
847F07BEDE4FA1F148930B02E2DF87F3A43112639C1987EF16F2230DD3F5E953
File Size:
20.49 KB, 20492 bytes
|
|
MD5:
e65b35b4c3f6a35fce45c03c2b888deb
SHA1:
c1926788651ca600e7a68f2cfa114842f5522c3e
SHA256:
4319F32F5F67DDEA45EE233F83626A11C50F5BF0691792D21D9406E887D0FD97
File Size:
20.49 KB, 20492 bytes
|
Show More
|
MD5:
ab7c7b8a544d803d6adbcde4aa5148d9
SHA1:
b000159b94aea39aafaeab5bd0f6c64c13ed3a2f
SHA256:
B389F4F44AA1BE244633B8D07BAECD373558C9E5403DE40FA63706554949FD2A
File Size:
20.49 KB, 20492 bytes
|
|
MD5:
f8656886052fdd02e99852ad7db19e6f
SHA1:
47ca0a582f370abcc38e309dea8c5327421ae59a
SHA256:
384EBA55CBA1896B11BB1B7D453AAC11F42856AB60B64C10995C026BDD194AEA
File Size:
20.49 KB, 20492 bytes
|
|
MD5:
12d197022a99655fe0942f6b3d019055
SHA1:
b77e7fb3ea531fbdb06dce9083df3be45050fa74
SHA256:
F8827DA1E0E704400D3911D6B6B990DA42880D582F92B716E8047C1F08428420
File Size:
20.49 KB, 20492 bytes
|
|
MD5:
d4f42e364a6547a32315e0b033744383
SHA1:
b8b94e2ed53f4ffc57fd212c529875892a022aa9
SHA256:
D0405B71FEA82DFFFAA8B19E9D0D26267DAD9817A20ECF36CF23658434B66D23
File Size:
20.49 KB, 20492 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have exports table
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Traits
- No Version Info
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 49 |
|---|---|
| Potentially Malicious Blocks: | 12 |
| Whitelisted Blocks: | 37 |
| Unknown Blocks: | 0 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Darkkomet.A
- Kryptik.XXF