iPhone Malware Can Spy on Desktop Keystrokes
 Several reports from within the online computer security industry have revealed that a team of Georgia Tech researchers have illustrated the ability of smartphones to spy on nearby desktop computers' keyboards. Apparently, a cleverly placed smartphone device and someone with the technological know-how can successfully employ the accelerometers of smartphones to spy on and track the activities occurring on a nearby desktop computer keyboard.
Several reports from within the online computer security industry have revealed that a team of Georgia Tech researchers have illustrated the ability of smartphones to spy on nearby desktop computers' keyboards. Apparently, a cleverly placed smartphone device and someone with the technological know-how can successfully employ the accelerometers of smartphones to spy on and track the activities occurring on a nearby desktop computer keyboard.
Typically, when discussing spyware in correlation to smartphone devices, such as the iPhone, security experts and researchers are usually referring to malicious software products utilized by hackers to steal sensitive data from the compromised devices or to eavesdrop on the device user's phone calls.
The interesting thing here, then, is the fact that a group of Georgia Tech researchers were able to successfully install spyware software onto smartphone devices that allowed them to spy on various activities occurring outside of the devices themselves.
Table of Contents
What the Georgia Tech Researchers’ Experiments Revealed
To be more precise, the Georgia Tech researchers were able to utilize the spyware software to track the activity of a regular desktop keyboard located near the spyware-enhanced smartphone.
This is a new twist on the concept of keystroke logging or using microphones to hear the specific keystrokes typed on a keyboard, and the team of researchers illustrated how malicious criminals could utilize this particular brand of new, spyware-based technology by planting a smartphone device near the keyboard of their marks. With this type of specialist spyware software, the criminals in question could utilize the planted smartphone to spy on the keyboard-related activity of their target.
One of the assistant professors from Georgia Tech's department of Computer Science, Patrick Traynor, remarked to reporters that, though this particular spying technique is a difficult technology to accomplish properly in order to get accurate and reliable results, today's smartphones are designed with built-in accelerometers that can reliably detect keyboard vibrations and decipher entire sentences typed with an accuracy of up to approximately 80%.
In fact, Traynor stated that: "We first tried our experiments with an iPhone 3GS, and the results were difficult to read, but then we tried an iPhone 4, which has an added gyroscope to clean up the accelerometer noise, and the results were much better. We believe that most smartphones made in the past two years are sophisticated enough to launch this attack." Accordingly, it is safe to assume that this remark applies to many of the newer iPhone and Android smartphones that are currently taking to mobile market by storm.
How Does This Particular Brand of Spyware Technique Work?
A hugely interesting aspect of the Georgia Tech researchers' experiments is the fact that the technique employed by the researchers to successfully snoop on the activities occurring on typical desktop computers' keyboards largely relied on probability.
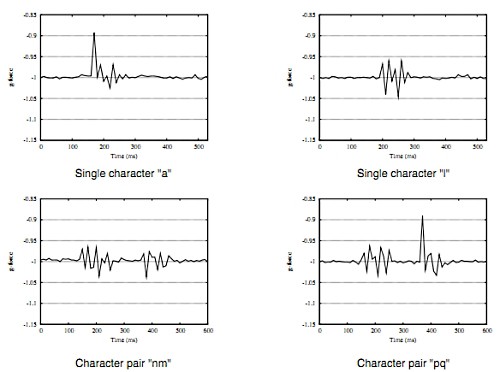
That is, the experiments' spyware product does not possess the ability to detect individual keys via the accelerometers of the iPhone; rather, the software works to detect "pairs of keystrokes" and determine which specific side of a typical QWERTY keyboard the keystrokes are located on (i.e. the right hand side or the left), as well as sense whether the pair of keystrokes detected are in close proximity to one another or located farther apart on the QWERTY-type desktop keyboard.
Once the spyware has collected each pair of keystrokes being typed on the targeted keyboard, the software then works to compare what has been collected against a dictionary that has assigned similar types of measurements to each word that it contains.
With the ability to only detect "pairs of keystrokes," rather than individually typed keys, this particular brand of spyware technique is only able to reliably work with words that require the pressing of three or more keystrokes; in other words, this particular type of spyware-based software is only reliable in terms of words that contain three or more letters.
newsofhacking.blogspot.com - Vibrations chart demonstrating single desktop keyboard characters recorded
Concluding Notes and a Few Questions
There is no arguing the fact that this research is incredibly interesting and innovative, but one has to wonder just how useful this software could be in real-life employment.
Passwords are often the number one target of malicious hackers that employ spyware to steal various kinds of confidential and sensitive information off of targeted computer systems, and in a lot of cases, targeted computer users sensibly employ reasonable security practices and their systems' passwords are not comprised of typical dictionary terms. In such cases, would this particular spyware technique be able to successfully decipher the systems' passwords?
What about numerical detections? Most of the financial data that is targeted by hackers, such as online bank account details and credit card numbers, contains a wide variety of numerals. Would this kind of spyware software be able to detect targeted information that contains numbers?
Additionally, it seems reasonable to suggest that most cyber criminals would be wary of employing a spyware technique that only guarantees an 80% accuracy rating.
The authors of this study also discussed the fact that the smartphone being employed to snoop must be located within three inches of the targeted keyboard. This leaves a large, gaping hole in the guarantee that this spyware product would successfully work. If the mark did something as simple as bump the spyware-loaded smartphone just a few inches away from the keyboard, this technique would not work successfully.
For these reasons, the Georgia Tech researchers behind this experiment concluded that the real possibility of this particular brand of spyware attack successfully working "right now is pretty low."
For more information, or if you are just simply interested in learning more about this study, the name of the paper produced by the Georgia Tech researchers is titled: "(sp)iPhone: Decoding Vibrations from Nearby Keyboards Using Mobile Phone Accelerometers."